10 Email Security Best Practices for 2026

Your team's biggest vulnerability is usually sitting in plain sight. It's in the inbox everyone uses all day, often with admin notices, client threads, invoices, shared docs, and automated alerts mixed together.
For a small team, one convincing message is enough. Someone clicks a fake client link, forwards the wrong file, or approves a request that looked normal in a rushed afternoon. If your team runs work through SaaS tools like Notion, the risk gets broader because email no longer lives in isolation. Messages trigger tasks, populate databases, notify contractors, and move customer data between systems.
That convenience is great for operations and dangerous for security if nobody has defined clear controls around it. A secure setup doesn't require an enterprise budget, but it does require discipline in the places small teams often skip: account access, sender authentication, attachment handling, permissions, and incident response.
These email security best practices focus on how small teams work today. They assume you're using cloud tools, shared workspaces, and lightweight automation. They also assume you need practical steps you can put in place without building a full security department. If you want a second perspective on the fundamentals, the CloudOrbis email security guide is a useful companion read.
1. Multi-Factor Authentication
Start with the control that prevents the most avoidable account takeovers. If a password gets reused, phished, or leaked, MFA gives you one more gate before an attacker gets into the mailbox.
For small teams, the biggest mistake isn't failing to understand MFA. It's rolling it out halfway. Admins are protected, but freelancers aren't. Shared inboxes are covered, but the marketing tool that sends on behalf of your domain isn't. Email security best practices fail fast when exceptions pile up.
What to enforce
Google Workspace and Microsoft 365 both support strong MFA policies, and that's where organizations should begin. Require MFA for every human account, every admin account, and every account that can send mail, manage domains, or connect to Notion workflows.
Use app-based time-based one-time passwords or hardware keys when possible. SMS is better than nothing, but it's weaker than app-based or device-bound options.
- Cover every role: Include founders, assistants, contractors, and anyone with inbox access or automation rights.
- Secure shared workflows: If someone manages a shared email database or sender settings, treat that account as high privilege.
- Prepare for lockouts: Store backup codes securely and assign a second recovery method before you enforce the policy.
MFA implementation roadmap is a solid operational reference if you need help sequencing rollout without locking out the whole team.
Practical rule: If a person can reset passwords, change DNS, approve invoices, or connect email to another app, that account needs stronger MFA than the minimum default.
One more thing matters here. Recovery flows are part of security. If your team bypasses MFA every time someone changes phones, people will start asking for weaker setups. Good MFA is strict, but it also has a clear recovery process that your ops lead can execute quickly.
2. Email Authentication SPF DKIM and DMARC
If your domain can be spoofed, attackers can impersonate your business without ever touching your internal systems. That's why SPF, DKIM, and DMARC belong near the top of any practical list of email security best practices.
For SaaS-heavy teams, this isn't just an IT task. Marketing platforms, CRM tools, support desks, and workspace-integrated email tools all send messages on your behalf. Every sender has to be authorized correctly, or you end up with a messy mix of legitimate failures and spoofing risk.

When you send emails from Notion, domain setup shouldn't be treated as an afterthought. If a tool supports custom domains and DKIM signing, use that support properly and document which services are allowed to send.
Where small teams usually stop too early
A lot of teams publish SPF and DKIM, then leave DMARC in monitoring mode forever. That leaves a gap between visibility and enforcement. According to the EU email authentication research summary, only 18.2% of the top 10 million domains maintain valid DMARC records, and just 7.6% actively enforce them with reject policies. The same source notes that strict enforcement reduces phishing risk across social engineering attacks.
That gap matters because monitoring alone doesn't tell receiving servers to block bad mail. It just tells you what happened after the fact.
- Start with visibility: Publish DMARC at
p=nonelong enough to identify all legitimate senders. - Fix every sender path: Update SPF, enable DKIM, and remove old tools still listed in DNS.
- Move to enforcement: Advance to quarantine or reject once reports show legitimate traffic is aligned.
Later in the rollout, show the team what "passing authentication" means in your mail platform. It reduces confusion when deliverability or vendor setup issues appear.
A quick visual walkthrough helps if your team hasn't configured these records before.
<iframe width="100%" style="aspect-ratio: 16 / 9;" src="https://www.youtube.com/embed/c9fLp5uIxp8" frameborder="0" allow="autoplay; encrypted-media" allowfullscreen></iframe>
3. End-to-End Encryption and TLS
Authentication proves who sent the message. Encryption protects what the message contains. Those are different jobs, and small teams often secure one while ignoring the other.
TLS should be your baseline for mail in transit. If your provider supports mandatory TLS settings for sensitive workflows, use them for financial documents, legal threads, HR messages, and customer data exports. For mail that carries highly sensitive content, S/MIME or PGP adds stronger message-level protection.
Match the method to the message
Not every team needs to encrypt every routine email end to end. Most don't. But every team should define which categories of messages require extra protection and which channels shouldn't use email at all.
A practical approach looks like this:
- Use TLS by default: Keep standard mail transport encrypted wherever your provider allows policy enforcement.
- Reserve E2EE for sensitive classes: Contracts, identity documents, health information, or privileged legal communications deserve stronger controls.
- Keep key management simple: If your team can't maintain certificates or keys reliably, limit E2EE to the users and workflows that can support it well.
Proton Mail and S/MIME-enabled enterprise mail systems are common examples of different encryption models. The trade-off is usability. Stronger encryption can add friction, especially when recipients use different mail clients or don't understand certificate prompts.
Strong encryption only helps when the sender knows when to use it and the recipient can actually open the message.
For teams using Notion-connected workflows, don't send raw sensitive exports into a shared database unless you've decided that database is an approved destination. Encryption should extend to the workflow design itself. Sometimes the safer move is to send a notification email and keep the sensitive file in a controlled portal instead of as an attachment.
4. Spam and Malware Filtering
A small team ships an onboarding update from Notion, a vendor reply lands in a shared inbox, and one malicious attachment gets opened before anyone notices. That is the core filtering problem for SaaS-heavy teams. Email is no longer a separate channel. It feeds shared docs, automations, ticket queues, and internal databases.
Filters need to catch more than obvious spam. They need to inspect the messages that look ordinary enough to pass a quick human check, then stop bad files and links before they touch the rest of your workflow. The VIPRE email threat trends report is a useful reference here because it tracks how attackers keep using everyday business themes, including invoices, shared documents, and account notices, to get clicks.
What to set up for a small team
Start with the controls your mail platform already offers, then tune them for how your team works. Microsoft 365 and Google Workspace both give small teams solid baseline filtering, but default settings are rarely enough if your team receives attachments from outside vendors, routes messages into Notion, or relies on shared inboxes.
Siteimprove's email security best practices article makes the right point: signature matching alone misses targeted attacks that use clean copy, trusted services, and low-volume sending patterns. Add behavior-based detection, link analysis, and attachment sandboxing if your provider supports them.
- Scan attachments before delivery or release: Pay close attention to ZIP files, Office documents, password-protected archives, and file types your team rarely uses.
- Inspect links at click time: Time-of-click analysis catches pages that were harmless when the email arrived but turned malicious later.
- Review quarantine every day: Assign one owner. If nobody owns releases and policy tuning, users start treating quarantine as random noise.
- Block unnecessary file types: Small teams often accept far more attachment formats than they need.
- Separate inbound review from workflow ingestion: If email content can create records in Notion or trigger automations, inspect it first and only pass through approved fields or attachments.
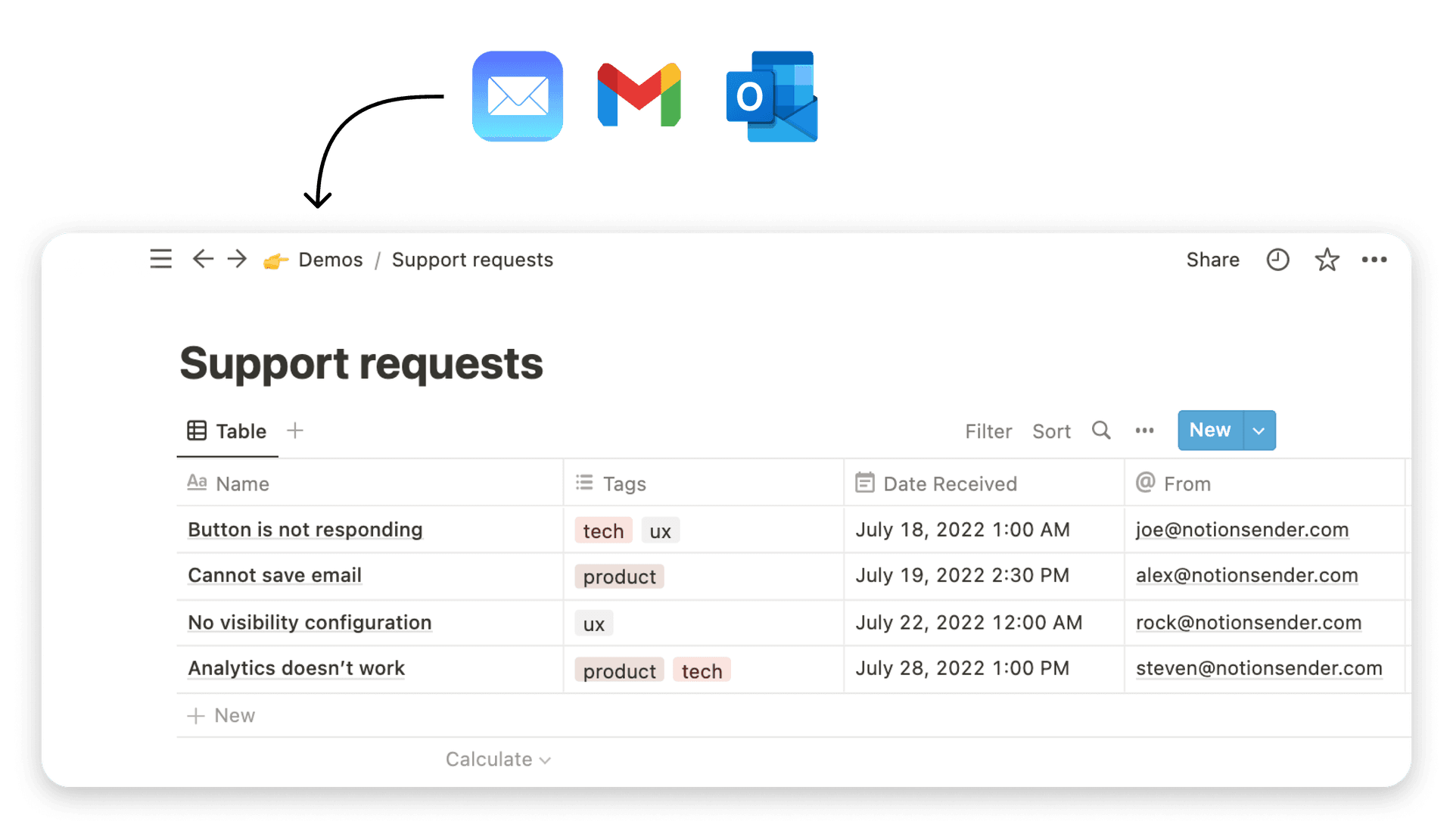
This matters even more in Notion-connected setups. If your team uses NotionSender or a similar tool to turn database activity into email workflows, keep the boundary clear. Outbound workflow automation should not become a path for risky inbound content to move into shared workspaces. A good starting point is this guide to successful email workflows for small teams using NotionSender.
One trade-off is false positives. Tight filters reduce exposure, but they can also delay contracts, invoices, and customer replies. The fix is not to loosen everything. It is to whitelist carefully, review misses, and tune policies around the senders and file types your team needs.
Microsoft Defender for Office 365, Mimecast, Proofpoint Essentials, and similar tools can all work. The deciding factor is operational discipline. Someone has to review alerts, adjust policies, and document what gets blocked, what gets released, and why.
5. Phishing Awareness and User Training
A coordinator gets an email that looks like a normal vendor follow-up. The sender name matches a real contact. The tone fits. The link goes to a fake login page, the password gets entered, and the attacker now has access to the same inbox that handles invoices, approvals, and Notion notifications.
That is why phishing training has to focus on decisions people make under time pressure, not on memorizing security trivia.

A small team usually does not need a full awareness program with long modules and quarterly quizzes. It needs a short, repeatable playbook. Check the sender context. Hover links before clicking. Treat requests involving payments, passwords, MFA codes, or shared document access as verification events. Report first, then ask questions in the right channel.
Google's guidance on avoiding phishing attacks makes the same point in practical terms. Users should verify unusual requests through a separate channel and pay attention to lookalike domains, unexpected attachments, and urgent language.
Training also needs to match the workflows your team runs. Finance staff should review fake invoice and bank-change requests. Hiring teams should see resume lures and calendar scam examples. Teams that run customer updates from Notion or trigger sends through tools like NotionSender should practice spotting fake approval emails, spoofed file-share notices, and credential prompts tied to shared workspaces.
Use real examples from your own inboxes, redacted if needed. That gets better results than generic phishing screenshots from a slide deck because people learn the patterns attackers use against your team, your vendors, and your SaaS stack.
A few habits make this stick:
- Create one reporting path: A suspicious email should go to a shared mailbox, help desk queue, or Slack channel with a clear owner.
- Run short simulations: Test common scenarios your team sees, then review misses without shaming people.
- Teach verification by role: Anyone who can approve payments, change bank details, share files, or reset accounts needs stricter checks.
- Document normal email patterns: If your team sends automated notices from Notion, publish examples of legitimate formatting, domains, and approval steps. This guide to successful email workflows for small teams using NotionSender can help define what your real outbound communication should look like.
There is a trade-off here. More caution slows people down. That is acceptable for high-risk actions such as payment changes, credential resets, and requests for confidential files. For routine messages, keep the process light so people will follow it.
One rule matters more than the rest. Do not punish fast reporting. If someone clicked and reported it within minutes, that helped the team. If they stay quiet because they expect blame, containment starts later and cleanup gets harder.
6. Role-Based Access Control and Least Privilege
Small teams often blur responsibilities because that's how small teams survive. The same person may run operations, update CRM records, send campaigns, and manage a shared inbox. That's efficient until one misconfigured permission exposes more than it should.
Least privilege fixes that by limiting who can do what. Not in theory. In the actual tools your team uses every day.
Scope access to the workflow
If someone only needs to review incoming messages saved to a Notion database, they don't need sender configuration rights. If a contractor needs to upload content for a newsletter, they don't need access to billing notices or API keys. Separate viewing, editing, sending, and admin permissions wherever your SaaS stack allows it.
API-connected email workflows deserve the same discipline. The Checkpoint analysis of the email security market shift notes that API-based email security represents about 15% of the market today, with projections of 40% to 50% within the next 3 to 5 years as cloud email becomes the standard model. For small teams, that means access control is increasingly about app permissions, tokens, and cloud roles, not just mailbox passwords.
- Map roles to real jobs: Admin, sender, reviewer, archive-only, and integration manager are more useful than broad default roles.
- Audit tokens and keys: Remove old API credentials tied to former staff or retired automations.
- Use temporary elevation: When someone needs emergency sending rights, grant them for a limited task and remove them after.
A lot of incidents that look external are really privilege design failures. Someone had access they didn't need, used the wrong account, or connected the wrong app because no one had drawn hard boundaries.
7. Data Loss Prevention
Not every email security failure starts with a malicious actor. A lot of damage comes from ordinary outbound mistakes. Someone sends the wrong attachment, copies the wrong contact, forwards internal notes externally, or pastes sensitive data into a routine reply.
This is why DLP matters. It catches what users miss when they're moving quickly.
Focus on accidental leakage, not just compliance
One of the more useful practical points in recent guidance is that recipient validation deserves more attention. The Hornetsecurity guide to email security best practices calls out sending sensitive content to the wrong person through autocomplete or manual address errors as a common cause of inadvertent data leaks. It also highlights policy controls such as blocking risky file types and scanning attachments before opening them.
That should change how small teams think about DLP. It's not only about formal patterns like card numbers or regulated records. It's also about catching the everyday operational mistakes that happen in customer-facing work.
- Warn on external recipients: Especially when a thread was previously internal.
- Require confirmation for sensitive attachments: Invoices, client exports, HR files, and internal reports deserve a second check.
- Block risky file types where possible: If your team never needs to send certain executable formats, don't allow them.
Field note: The most common outbound email problem on small teams isn't espionage. It's someone sending the right message to the wrong person.
If your workflow sends from different databases or functions, apply different DLP rules by use case. Billing, support, recruiting, and project delivery don't carry the same risk profile. One policy for all outbound mail usually becomes either too weak or too disruptive.
8. Email Archiving and Backup
If a mailbox is deleted, a message thread disappears, or a team member leaves abruptly, can you recover the record cleanly. Many teams assume their email provider handles this automatically. Sometimes it does, sometimes it partly does, and sometimes retention settings were never configured at all.
Archiving is different from keeping a big inbox. It creates a reliable historical record that people can't casually edit or erase. That's useful for disputes, continuity, audits, and incident investigation.
Build a record you can trust
Google Vault, Proofpoint archive products, and similar systems are common examples. The principle is simple. Preserve messages in a way that survives account changes and supports search.
For Notion-centered operations, one practical pattern is to save emails to Notion in a read-only archive database while keeping the primary retention system in your mail platform or archive tool. That gives operators visibility without making the archive itself easy to alter.

A useful archive policy usually includes:
- Clear retention windows: Keep messages based on legal, contractual, and operational needs.
- Read-only storage for records: Don't let routine users modify the historical copy.
- Restore testing: Prove that a deleted or lost thread can be recovered.
Archiving also helps with investigations. If someone reports a suspicious message after it's been deleted from the inbox, your team still needs access to headers, timestamps, and related conversation context. Without that record, response gets slower and guesswork increases.
9. Secure Configuration and Patch Management
A secure email environment isn't just about inbox settings. It's also about every connected component staying current and tightly configured. Mail clients, browser extensions, identity providers, SMTP relays, DNS settings, forwarding rules, and third-party integrations all create openings when they drift.
Many understand that patching matters. The harder part is knowing what belongs on the patching list.
Treat misconfiguration like a real threat
Start with an inventory. List your mail provider, add-on tools, browser extensions used for email, sending services, shared mailbox delegates, mobile mail clients, and every app with inbox or send permissions. Then decide who owns each one.
Good hardening usually includes removing stale forwarding rules, disabling legacy authentication, limiting mailbox delegation, and reviewing app permissions that grant read or send access. If you run any self-hosted mail components or custom relays, patching should follow a regular maintenance window with rollback plans, not ad hoc updates after someone notices an issue.
- Subscribe to vendor advisories: Email, identity, and integration tools all publish security notices.
- Use baseline configurations: Standardize settings so new accounts don't inherit weak defaults.
- Remove what you don't use: Unused plugins and abandoned connectors increase attack surface without giving you anything back.
This is one of the least glamorous email security best practices, but it pays off. Attackers often don't need a novel technique when an old token, weak setting, or forgotten plugin is still available.
10. Security Monitoring and Incident Response
A founder gets a complaint that customers received a strange message from the team inbox. In the same hour, someone notices a new forwarding rule on the support mailbox and an unfamiliar OAuth app connected to Google Workspace. At that point, prevention has already failed. The job is containment.
Security monitoring for email should center on the few signals that usually show up before real damage spreads. Watch for logins from impossible locations, repeated MFA failures, mailbox rule changes, unusual outbound volume, mass message deletes, new app authorizations, and DNS changes that affect SPF, DKIM, or DMARC. For small teams running Gmail or Microsoft 365 alongside SaaS tools like Notion, these events often tell a clearer story when viewed together than in separate admin panels.
Microsoft documents common signs of business email compromise and the investigation steps defenders should take, including checking inbox rules, sign-in activity, transport rules, delegate access, and consented applications in Microsoft 365. That guidance is useful even if your stack is not fully on Microsoft, because the attacker behavior is usually similar across cloud mail systems.
Build a response plan that fits a small team
A usable incident plan can stay short. It should answer five questions fast: who locks the account, who reviews email and identity logs, who checks DNS and sending tools, who pauses automated workflows, and who handles customer communication.
That last point matters more in SaaS-heavy setups. If your team uses Notion to trigger outbound email, store support context, or hand off work between tools, an email incident can spill into docs, databases, and automations quickly. A compromised mailbox tied to NotionSender or another sending layer is not just an inbox problem. It can affect templates, recipient lists, workflow permissions, and audit trails.
Use a runbook with concrete actions:
- Contain the account: Revoke sessions, reset credentials, require MFA re-registration if needed, and remove suspicious app consent.
- Check for persistence: Review forwarding rules, delegates, shared mailbox access, transport rules, and API tokens tied to email workflows.
- Pause risky automation: Stop outbound campaigns, notification flows, or Notion-based triggers until you confirm what was touched.
- Preserve evidence: Export sign-in logs, admin audit logs, message traces, and DNS records before cleanup changes overwrite the trail.
- Communicate in order: Internal owners first, affected customers next, legal or compliance contacts if your obligations require it.
Run one tabletop exercise every quarter. Use a realistic scenario, such as a phish that reaches a shared inbox and then triggers a Notion workflow that exposes customer data to the wrong teammate. Small teams do not need a full SOC to do this well. They need clear ownership, a short checklist, and enough practice that nobody is deciding basic steps under pressure.
Fast response limits the blast radius. Calm, boring execution usually beats clever improvisation.
10-Point Email Security Comparison
| Security Measure | 🔄 Implementation Complexity | ⚡ Resource Requirements | 📊 Expected Outcomes | 💡 Ideal Use Cases | ⭐ Key Advantages |
|---|---|---|---|---|---|
| Multi-Factor Authentication (MFA) | Moderate, enroll users, integrate SSO/conditional access | Low–Moderate, auth apps, hardware tokens, support effort | Strong reduction in account takeover; blocks most automated attacks | Protect admin/privileged accounts and any user-facing email access | High effectiveness; flexible factors; low residual risk |
| Email Authentication: SPF, DKIM & DMARC | Moderate–High, DNS changes and DMARC tuning | Low, DNS access plus monitoring tools for reports | Improved deliverability and reduced domain spoofing | Public-facing domains, bulk senders, brand protection | Concrete anti-spoofing + visibility via reports |
| End-to-End Encryption (E2EE) & TLS | High, key/certificate management and client support | Moderate–High, PKI, certificates, user guidance | Confidentiality in transit and at rest; regulatory alignment | Sensitive communications, healthcare/finance, compliance needs | Strong data confidentiality and integrity |
| Spam & Malware Filtering | Moderate, integration and ongoing tuning | Moderate, threat feeds, sandboxing, licensing | Fewer malicious attachments and phishing links; less inbox clutter | High-volume environments and externally-facing mailflows | Automated threat blocking; reduces ransomware/credential theft |
| Phishing Awareness & User Training | Low–Moderate, program setup and simulated campaigns | Low, training platform, time for staff participation | Lower click-through rates; improved reporting behavior | SMBs and distributed teams as complement to technical controls | Reduces human risk; identifies high-risk users for coaching |
| Role-Based Access Control (RBAC) & Least Privilege | Moderate, define roles, scope API keys, periodic audits | Low–Moderate, admin time and tooling for groups | Reduced blast radius from compromised accounts; cleaner audits | Teams with many users, contractors, or API integrations | Limits privileges; simplifies compliance and separation of duties |
| Data Loss Prevention (DLP) | High, granular rule creation and tuning | Moderate–High, content engines, scanning compute | Prevents accidental data leaks; supports compliance reporting | Regulated industries, PII/financial data workflows | Automated inspection and policy enforcement |
| Email Archiving & Backup | Moderate, integrate retention, indexing, WORM storage | Moderate, storage costs, indexing services, restore tests | Recoverability, legal defensibility, audit trail preservation | Compliance-driven orgs and those needing forensic history | Tamper-proof archives; fast restores for incidents |
| Secure Configuration & Patch Management | Moderate–High, baselines, coordinated updates, testing | Moderate, scanners, staging environments, change windows | Reduced exploitable vulnerabilities; audit evidence | Self-hosted components, servers, and critical infrastructure | Proactively closes security gaps; enforces best-practice baselines |
| Security Monitoring & Incident Response | High, SIEM integration, alerting, playbooks | High, security analysts, log retention, tooling | Early detection and faster remediation; reduced dwell time | Organizations requiring 24/7 visibility or high-risk profiles | Rapid detection/forensics and structured incident handling |
Turn Security from a Chore into a Habit
The strongest email security best practices aren't the flashiest ones. They're the controls your team uses every day without shortcuts. MFA that nobody can bypass casually. Authentication records someone reviews. Permissions that reflect real roles. Filtering that gets tuned instead of ignored. Training that helps people make better decisions in the middle of real work.
Small teams usually don't need more theory. They need tighter execution around the systems already running the business. That's especially true when email is connected to a workspace like Notion, where one message can trigger follow-up actions, populate a database, or expose internal context to the wrong person. The workflow is the security boundary now, not just the mailbox.
If you're prioritizing, start with the few controls that reduce the most risk fastest. Turn on MFA everywhere. Audit who has access to sending tools and shared inboxes. Publish SPF and DKIM correctly, then move DMARC from monitoring toward enforcement when you understand your email sending environment. Review your attachment and recipient controls, because not every damaging email event is a phishing success. Many are ordinary mistakes made under time pressure.
After that, build consistency. Assign ownership for quarantine review, DNS records, archive retention, and incident response. Document where email enters your Notion workflows, where it gets stored, and which automations can act on it. If nobody owns those paths, security gaps will stay invisible until something breaks.
It's also worth being realistic about trade-offs. More security can add friction. Encryption can confuse recipients. DLP can slow down sending. Least-privilege access can frustrate people who were used to broad permissions. That's normal. The goal isn't zero friction. The goal is deliberate friction in the places where mistakes are expensive.
For teams that already use Notion as an operating system for projects, support, or client work, a tool like NotionSender can fit into a secure process if it's configured carefully. Validate domains, limit access, define how inbound messages are stored, and avoid treating convenience settings as harmless defaults. That's the pattern that holds up over time.
Security becomes manageable when it turns into routine maintenance instead of a once-a-year cleanup project. Pick two changes this week. MFA and DMARC monitoring are a good start. Then keep going until secure email handling feels normal to everyone on the team.
If your team runs work inside Notion, NotionSender is one way to bring email into that workflow. Review how it handles sender validation, inbound routing, permissions, and database storage, then configure it to match the security controls your team already expects from the rest of its SaaS stack.