A Guide to the Cyber Security Domain for Your Business

So, what exactly is a cyber security domain?
Think of it as a specific discipline within the massive world of digital protection. Just like medicine has specialized fields like cardiology for the heart and neurology for the brain, cyber security has its own areas of focus—like network security, data protection, and incident response.
Why Cyber Security Is a Core Business Strategy
Cyber security has officially moved out of the IT department's basement and into the boardroom. It’s no longer a technical afterthought; it's a fundamental part of your business strategy, every bit as critical as finance, sales, or marketing.
Imagine your digital footprint—your website, customer lists, and cloud apps—as a physical storefront. You wouldn't dream of leaving the doors unlocked all night with the cash register sitting wide open, right? That’s exactly how you need to start thinking about your digital assets.
Every email you send, every file you upload to the cloud, and every transaction you process is a potential entry point for an attack. This is the new reality for project managers and small business owners. You are now the first line of defense, the primary security guards for your own digital operations.
The New Reality of Digital Threats
If you want a sense of the scale of this challenge, just follow the money. Global spending on cybersecurity is projected to hit an eye-watering $454 billion by 2025. That represents a massive 74.6% jump from 2021.
This isn't just random spending. This explosive growth reflects a simple, unavoidable truth: threats are multiplying, and a proactive defense is the only way to survive. This shift means building a security-first culture isn't just a "nice-to-have." It directly impacts your revenue, your reputation, and your company's long-term survival. Understanding how modern frameworks like What Is SOC 2 Compliance help build that customer trust is a great place to start.
Protecting your company is not just about buying software; it's about building a 'human firewall.' This starts with understanding that every team member, from the CEO to an intern, plays a role in defending the business.
This guide will give you the foundational knowledge to build a security plan that's both practical and effective. You don’t need a deep technical background—just a commitment to protecting what you’ve worked so hard to build. By walking through each cyber security domain, you’ll be able to make informed decisions that secure your business's future.
Mapping Your Cyber Security Domain Landscape
To really get a handle on security, you have to know the lay of the land. The term "cyber security" can feel like a giant, intimidating concept, but it's not one single thing. It’s actually a collection of different security fields, each one guarding a specific part of your business.
Thinking of security this way—as separate areas or domains—is the key to making it manageable. Instead of trying to "be secure" all at once, you can focus on strengthening one area at a time. It breaks a huge challenge down into bite-sized pieces.
For example, Network Security is a bit like the locks, gates, and security guard at your office building. It’s all about controlling who can get in and out of your digital space. Then you have Cloud Security, which is more like securing a high-tech storage unit you rent from a company like Amazon Web Services or Google Cloud. You have to make sure your unit is locked up tight, even though someone else owns the building.
The Core Areas of Digital Protection
These domains don't exist in a vacuum; they all work together. A weakness in one domain can create an opening for an attacker to get into another, which is why seeing the whole picture is so critical. You don’t need to be an expert in every single one, but understanding what they do is the first step toward building a solid defense.
This diagram shows exactly how cyber security fits into the bigger picture, acting as a foundational layer for your entire business strategy.

As you can see, good security isn't just an IT problem—it’s a business strategy. It's what protects the value you're working so hard to create.
To help you get started, here's a quick reference table that breaks down the main security domains with a simple analogy for each one.
Your At-a-Glance Guide to Cyber Security Domains
Use this table to quickly understand the core cyber security domains, their main purpose, and a simple analogy to grasp their role in your business.
| Security Domain | What It Protects | Simple Analogy |
|---|---|---|
| Network Security | Your internal networks, Wi-Fi, and connections to the internet. | The walls, fences, and gates around your business property. |
| Application Security | The software and apps your team uses every day. | Inspecting every tool and piece of equipment for safety hazards before use. |
| Cloud Security | Your data and services hosted on platforms like AWS or Google Cloud. | Securing the specific storage unit you rent in a large, shared facility. |
| Data Protection | Your sensitive information (customer lists, financial records, etc.). | The safe inside your office where you keep your most valuable documents. |
| Endpoint Security | Individual devices like laptops, phones, and servers. | Putting a security guard and camera on every single door and window. |
| Identity & Access | User accounts, passwords, and permissions. | The keycard system that controls which employees can enter which rooms. |
| Incident Response | Your plan for reacting to a security breach. | The fire drill and emergency evacuation plan for your building. |
| Governance & Compliance | The rules and policies that guide your security efforts. | The company handbook that outlines all safety procedures and rules. |
This table gives you a bird's-eye view, but let's quickly touch on a few of the most important domains every business and project team needs to think about.
Key Domains Every Business Should Know
Beyond just networks and the cloud, a few other domains are absolutely essential for protecting your day-to-day operations.
Here’s a quick rundown of the big ones:
- Application Security: This is all about the software your team relies on, whether it's your CRM, project management tool, or accounting platform. The goal is to make sure the apps themselves don't have holes that an attacker could slip through.
- Data Protection: This one’s straightforward—it’s about protecting your most valuable information. Think customer data, financial reports, or internal strategy documents. A big part of this is encryption, which basically scrambles your data so it’s unreadable to anyone who shouldn't see it.
- Identity and Access Management (IAM): This domain is all about who gets to do what. It covers user accounts, passwords, and permissions to ensure that people only have access to the information and tools they absolutely need to do their job. Nothing more.
- Incident Response: This isn't about stopping an attack; it's about what you do when one happens. It’s your game plan for reacting quickly, containing the damage, and getting back to business as fast as possible.
Think of it like the security at a museum. You have guards at the doors (Network), alarms on the paintings (Data Protection), and a detailed plan for what to do if a thief actually gets inside (Incident Response). Each system plays a different, vital role.
Now that you have a map of the territory, we can start digging into the details. In the next sections, we'll explore each of these domains and show you practical actions you can take to start securing your business today.
Securing Your Digital Doors and Windows
Alright, now that we understand the lay of the land, it's time to start building our defenses. The first and most critical place to focus on is your digital perimeter—think of it as all the doors and windows to your business. This foundational layer is protected by three security areas that work hand-in-hand: Network, Endpoint, and Application Security.

It helps to think of these three as a team. Network Security is like the fence and gate around your property. Endpoint Security protects every individual room inside the building. And Application Security makes sure the tools you use inside those rooms are safe. When they all work together, they create a seriously tough barrier against most attacks.
Locking Down Your Network
Your network is the digital front door to your business. Network Security is all about controlling who gets to walk through it. This is your absolute first line of defense, and getting it right is non-negotiable.
For most small businesses and teams, this boils down to two simple but powerful actions:
- Secure Your Wi-Fi: Use a strong, complex password and enable WPA3 encryption if your router supports it. You should also create a separate "guest" network for visitors, so their devices never get a chance to touch your main business network.
- Use a Firewall: Your internet router already has a firewall built-in. Picture it as a digital bouncer, checking IDs at the door and turning away anyone who looks suspicious. Just make sure it's turned on and configured.
These two steps are the digital equivalent of putting a solid deadbolt on your front door. They won't stop a highly skilled professional, but they will absolutely deter the vast majority of casual, opportunistic threats.
Guarding Every Device
Once someone gets past the main gate, you need security on every door and window inside. This is where Endpoint Security comes in. An "endpoint" is simply any device connected to your network—laptops, smartphones, tablets, even servers.
Every single unprotected device is an open window for an attacker. It's a sobering fact that a staggering 95% of cybersecurity breaches involve human error, often starting with a compromised endpoint.
Protecting these devices is a must. Your game plan should be to install reputable antivirus and anti-malware software on every single device, no exceptions. Even more importantly, enable automatic software updates for operating systems and all your apps. These updates frequently contain crucial security patches for newly found vulnerabilities.
Vet Your Software and Tools
Finally, Application Security zeroes in on the software your team relies on every single day, from your CRM to your project management tools. It turns out that exploits in third-party applications are a very common way for attackers to get in. A big part of this is managing how apps connect to each other through APIs, which you can see in action with resources like the NotionSender API documentation.
A great habit to build is vetting any new software before you start using it. Look at its security features, read reviews, and get a clear picture of what data it will access. It's also smart to routinely check the permissions for all your third-party apps, making sure they only have access to what they absolutely need to function.
Alright, once you've shored up your digital perimeter, it’s time to focus on what’s inside: your data, and who gets to touch it. This is where two critical security domains come into play: Data Protection and Identity and Access Management (IAM). Think of them as working together to guard your most important information from both outside attacks and internal mistakes.

Data protection is like the digital version of a bank vault. Even if someone manages to slip past the front door, your most valuable assets—customer lists, financial records, secret sauce recipes—are still locked away safely. The two main tools for this are encryption and backups.
Encryption scrambles your data, turning it into unreadable gibberish for anyone who doesn't have the specific key. Backups are your safety net, ensuring you can restore everything if data is ever lost, stolen, or held for ransom.
A fantastic starting point is the simple “3-2-1 backup” strategy: keep three copies of your data, on two different types of media, with one copy stored completely off-site. For a deeper dive into putting this into practice, this guide on Data Security Management offers some great, practical insights.
Controlling Who Has the Keys
While data protection builds the vault, Identity and Access Management (IAM) is the system that decides who gets a key and which doors it can open. The whole point of IAM is to make sure the right people have the right access to the right tools, at the right time. Its guiding idea is the principle of least privilege.
It’s a simple concept: only give people the absolute minimum access they need to do their jobs. An intern doesn't need to see payroll, and a marketing specialist shouldn’t be able to tinker with your website's code.
A huge piece of IAM is Multi-Factor Authentication (MFA). Just by requiring a second verification step, like a code from a phone app, you can block over 99.9% of automated attacks that try to compromise accounts. It's one of the single most powerful security moves you can make.
The Central Role of Email Security
You can't talk about protecting data and access without talking about email. It’s still the number one way attackers get into businesses, with phishing—those deceptive emails designed to steal your login info or drop malware—as the main weapon. Attackers love going after individual inboxes because they're scattered and difficult to monitor centrally.
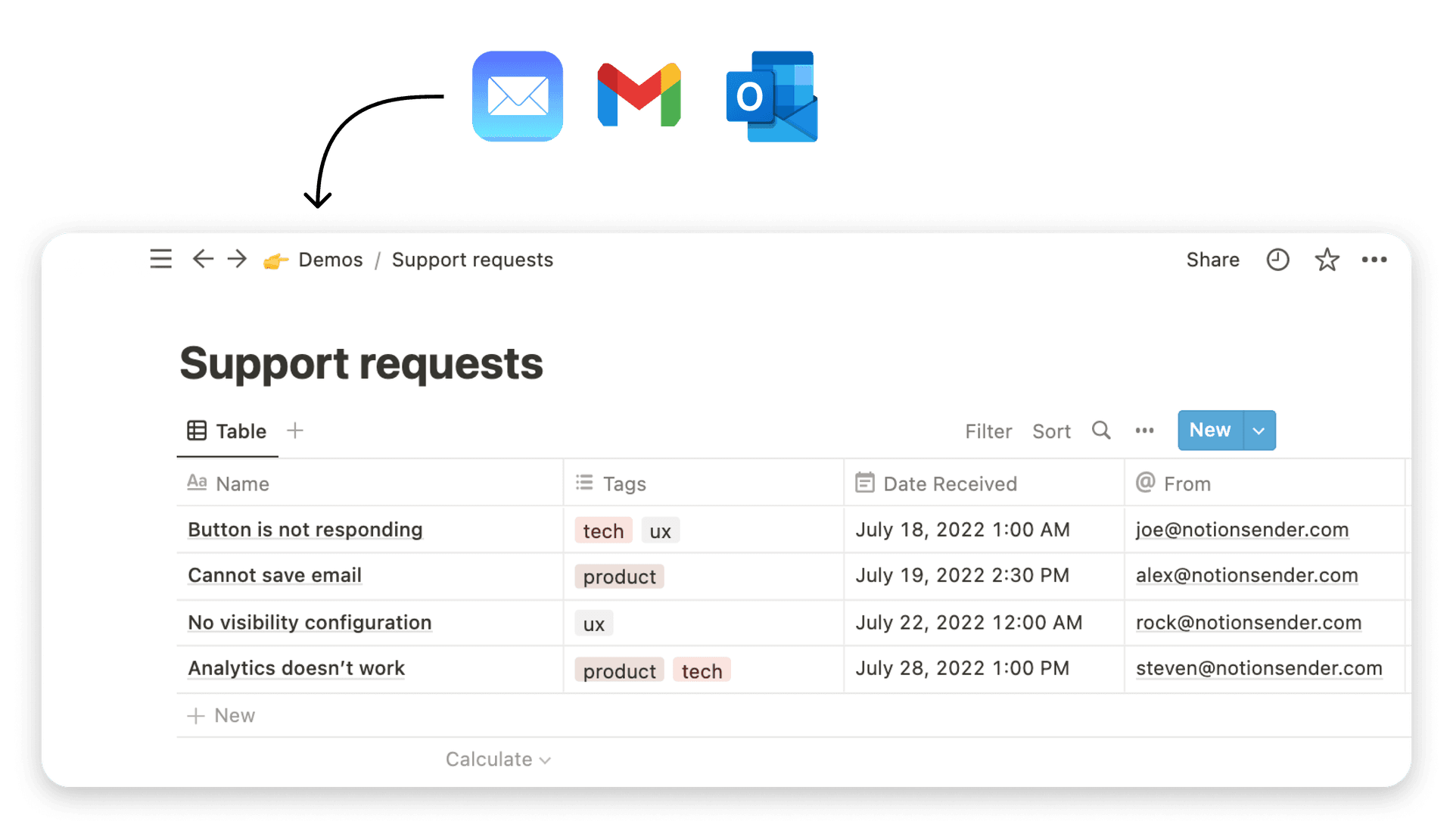
This is why centralizing your communications can make a massive difference. When your team's email workflows are pulled into a single, unified system, it's far easier to spot weird activity and patch up weak spots.
To see how you can bring email into a more controlled workspace, take a look at our guide on how to send emails to Notion. This approach doesn't just tighten up security; it also makes your team more productive by keeping project data and conversations all in one place.
Even with the best defenses in place, a security breach can still happen. That’s why a smart cyber security strategy isn't just about building walls—it's about knowing what to do when one of those walls gets knocked down.
This is where two absolutely critical domains come in: Incident Response and Governance, Risk, and Compliance (GRC). Think of it like this: a skyscraper has fire alarms, sprinklers, and a clear evacuation plan. IR and GRC are your business's digital fire drill and safety code, making sure you can handle an emergency and get back on your feet quickly.
Mastering Your Incident Response Plan
An Incident Response (IR) plan is your step-by-step playbook for the moment you suspect a security issue. A solid plan turns a moment of panic into a structured, calm, and effective reaction. The goal is always to find the threat, contain the damage, and get back to business as usual, fast.
Without a plan, the average time to contain a breach is a staggering 73 days. When a team has a rehearsed plan, that time shrinks dramatically, saving you from painful downtime and damage to your reputation.
Your plan doesn't have to be a novel. A simple one-page document is a thousand times better than nothing. It just needs to clearly outline a few things:
- Detection: How will you know something is wrong? This could be an alert from your security software or a team member spotting something unusual.
- Containment: What’s the first move to stop the problem from spreading? Usually, this means disconnecting the affected computer or account from the network.
- Eradication and Recovery: How do you get the threat out and restore your systems from a clean backup?
- Communication: Who needs to know, and when? This includes your IT support, key people on your team, and maybe even your customers.
Think of your Incident Response plan as a fire drill. You don't wait for a fire to figure out where the exits are; you practice beforehand so everyone knows exactly what to do. The same idea applies to a cyber attack—preparation is everything.
Establishing Your Security Rulebook
While Incident Response is all about reacting to a crisis, Governance, Risk, and Compliance (GRC) is the framework that guides your entire security strategy. It's your company's official security rulebook. This domain makes sure your security efforts are consistent, effective, and in line with any legal requirements you have.
GRC means setting clear internal policies, knowing your legal duties (like GDPR if you have customers in the EU), and regularly checking for risks. The security market keeps growing because this kind of planning is no longer optional. Research on the expanding needs of the cybersecurity market shows that smart businesses are investing in integrated security, which includes having a rock-solid response plan.
A strong governance framework is what separates businesses that bounce back from a security incident from those that don't. It makes sure everyone in your organization knows their role in keeping things secure, creating a security-first culture that becomes your most powerful defense.
Your First Cyber Security Action Plan
Alright, we've talked a lot about what these cyber security domains are. But theory only gets you so far. Now it's time to turn that knowledge into action.
Think of this section as your starter checklist. It's a practical guide to get you from learning about security to actually doing it. Bookmark this page and work through it one step at a time. The goal here is steady progress, not trying to boil the ocean overnight.
Foundational Security Quick Wins
Let's start with the low-hanging fruit—the simple actions that give you the most security bang for your buck. These steps shore up your digital perimeter and protect the places attackers hit most often.
-
Endpoint & Email Security: Turn on Multi-Factor Authentication (MFA) for all your critical accounts. I’m talking about email, banking, your main CRM—anything important. Microsoft’s data shows that MFA can stop over 99.9% of automated attacks trying to break into your accounts.
-
Network Security: Set up a separate Wi-Fi network just for guests and personal devices. Give it its own password. This one simple move puts a wall between your core business network and any untrusted devices, instantly shrinking your attack surface.
-
Application Security: Make a quick list of all the software and third-party apps your team uses. Go through and check what permissions they have. If an app isn't used anymore or asks for way more access than it needs, get rid of it.
Getting these first few steps done is like locking your digital doors and windows. It’s the commonsense stuff you do before you even think about installing a fancy alarm system. You’re immediately closing the most common ways attackers try to get in.
Building Your Security Operations
With the basics in place, we can start building some simple, repeatable processes. This is all about creating a playbook so your security efforts become a reliable system, not just a one-off task. These next steps map directly to the Governance and Incident Response domains we discussed.
-
Draft a Simple Incident Response Plan: This doesn't need to be a novel. Start with a one-page contact sheet. Who do you call first if something goes wrong (your IT guy, a tech-savvy friend)? What's the very first step to take (like yanking the affected computer off the internet)? Having a plan ready saves you from panicking.
-
Establish a Data Backup Schedule: The "3-2-1" rule is your best friend here. Keep three copies of your important data, on two different types of storage, with at least one copy stored safely off-site (the cloud is perfect for this).
-
Define Access Controls: Take a hard look at who can access sensitive company files. Start applying the "principle of least privilege"—if someone doesn't absolutely need access to something to do their job, they don't get it. It’s that simple.
A Few Common Questions About Business Cyber Security
Diving into cyber security can feel like a lot, especially when you're trying to figure out all the different ways to protect your business. Most business owners have the same practical questions: Where do I even start? How much is this going to cost? And what actually makes a difference?
Let's clear things up with some straight answers.
Where Should a Small Business Start?
If you're looking for the single best first step, focus on the areas with the highest risk. For almost any business out there, that means starting with Endpoint and Email Security.
Think about it—you need to secure the devices your team uses every single day (their laptops and phones) and the main way you all communicate (email). Locking these down immediately defends against the most common attacks you'll see, like malware and phishing scams.
Nailing this one cyber security domain first gives you the biggest bang for your buck, right away.
How Much Should We Budget for Security?
There's no single magic number here, but a good rule of thumb is to set aside 3-6% of your total IT budget specifically for security. You don’t need to go out and buy a suite of expensive tools from day one.
Instead, start with the low-cost actions that have a huge impact:
- Switch on Multi-Factor Authentication (MFA) for every critical account.
- Get your team up to speed on how to spot a sketchy phishing email.
- Set up a reliable data backup plan.
As your business gets bigger, you can start looking into more sophisticated tools. To get a better sense of how all the pieces fit together, take a look at our guide on email and project management security.
Don't sleep on creating a simple incident response plan. Seriously, even a one-page document that lists key contacts and the first few steps to take is a game-changer. A plan turns sheer panic into a clear, structured response, which can save you a ton of time and money when it counts.